Access Management , Privileged Access Management , Security Operations
Automated Cyber Defense: Leveraging Identity Management to Get to Acceptable Losses

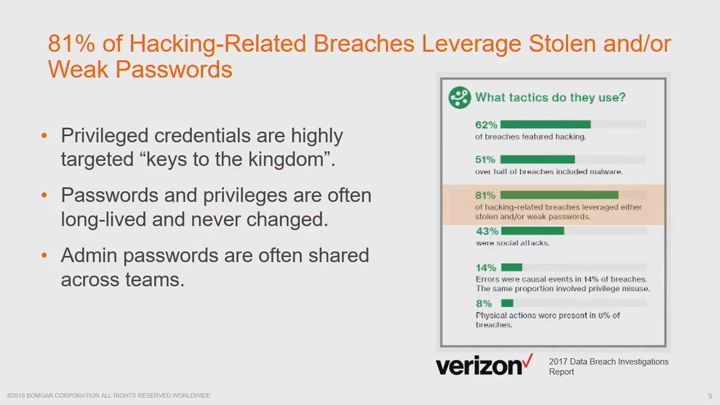
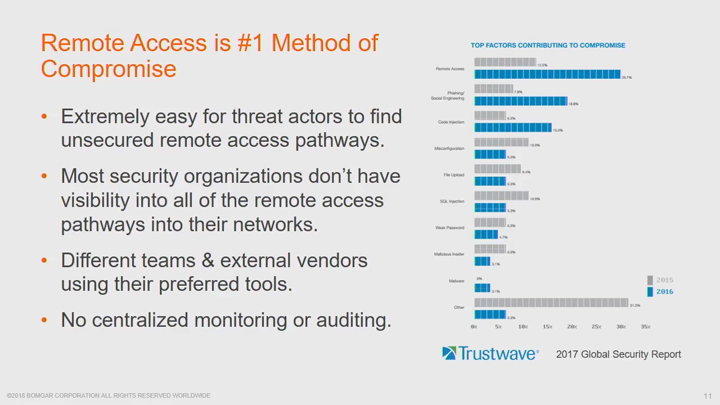
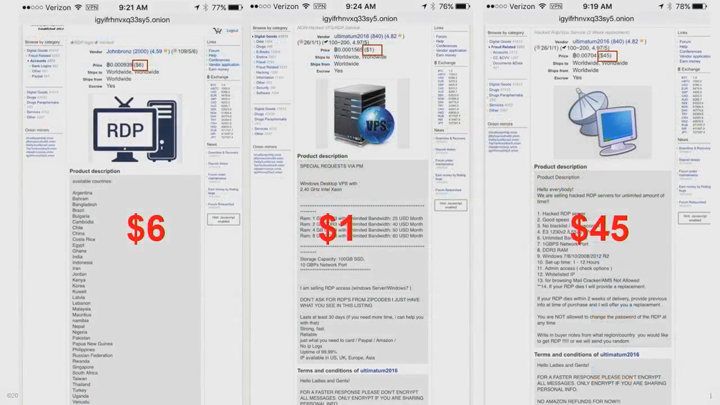
Today's world of cyber warfare is one of continuous zero-day attacks, targeted phishing scams and malicious insiders. Anyone trying to deal with these threats manually has already lost the game. You can't stop cyberattacks from occurring. But, you can significantly limit the damage when these inevitable attacks strike.
See Also: Advancing Zero Trust with Privileged Access Management (PAM)
Based on his years of extensive real-world experience, Sam Elliott will cover how to redesign and automate your organization's identity management (especially privileged identities and access) to achieve acceptable losses, even while under constant cyberattack. Among the takeaways:
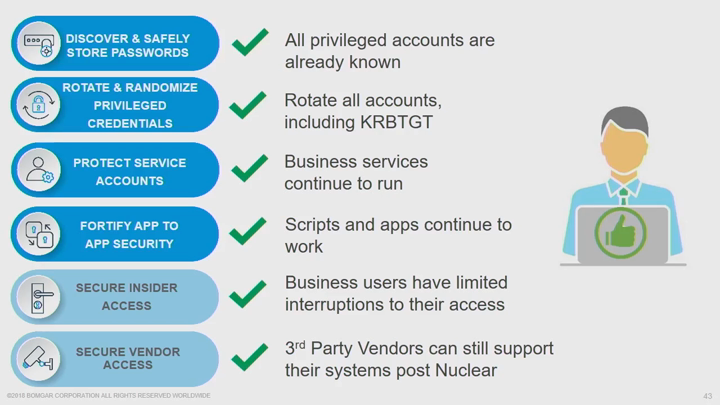
- You can't eliminate breaches, but you can contain their impact to acceptable loss.
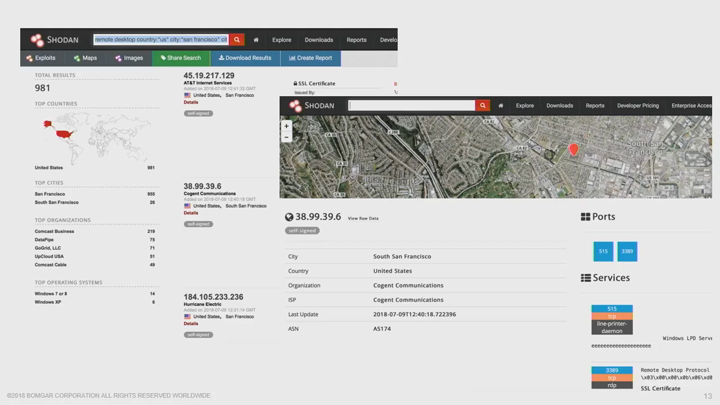
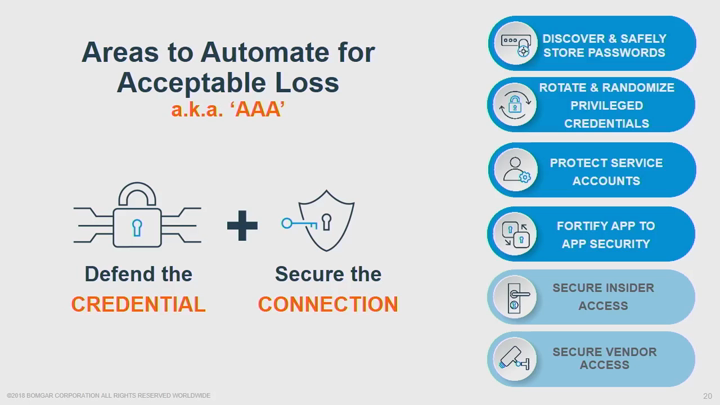
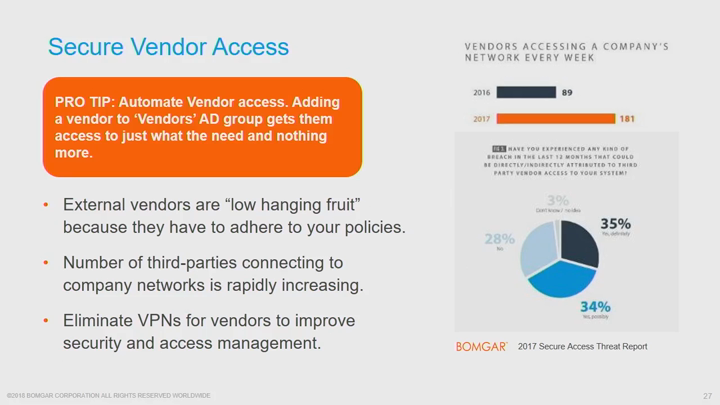
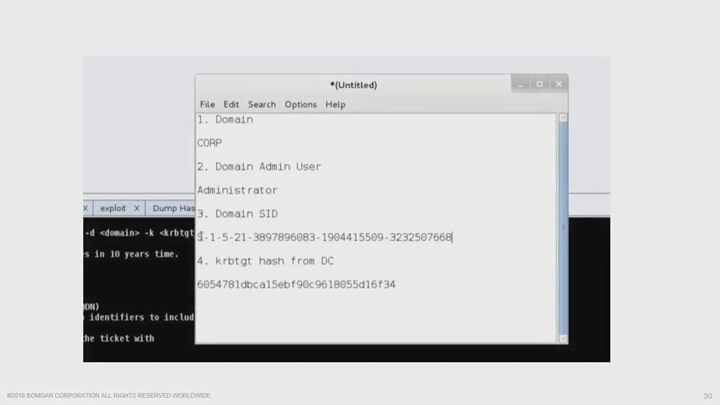
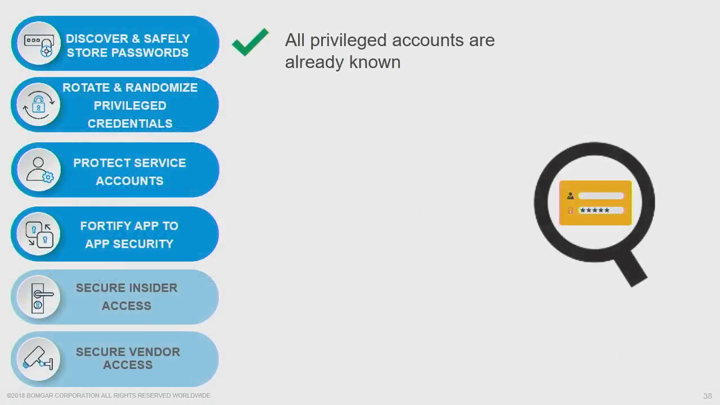
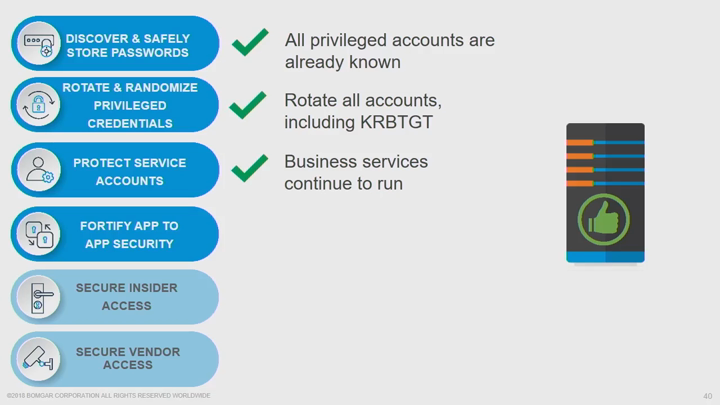
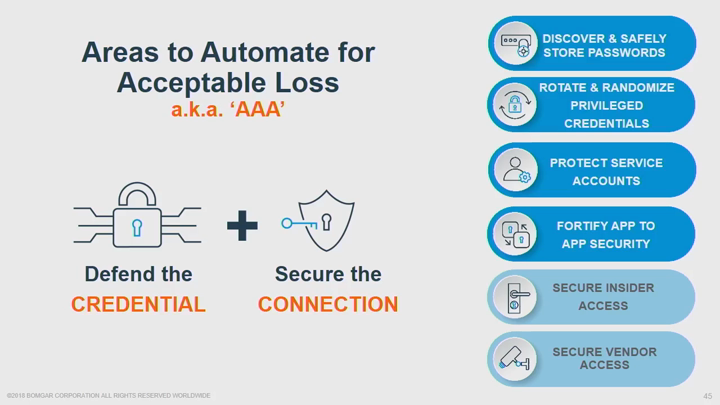
- By protecting both privileged identities and access pathways you can mitigate the damage done by attackers.
- Using security automation will allow you to protect yourself against threats while increasing business productivity and performance.