Multi-factor & Risk-based Authentication , Next-Generation Technologies & Secure Development
Verizon: Most Breaches Trace to Phishing, Social Engineering
Chris Novak Says Too Few Organizations Use MultiFactor Authentication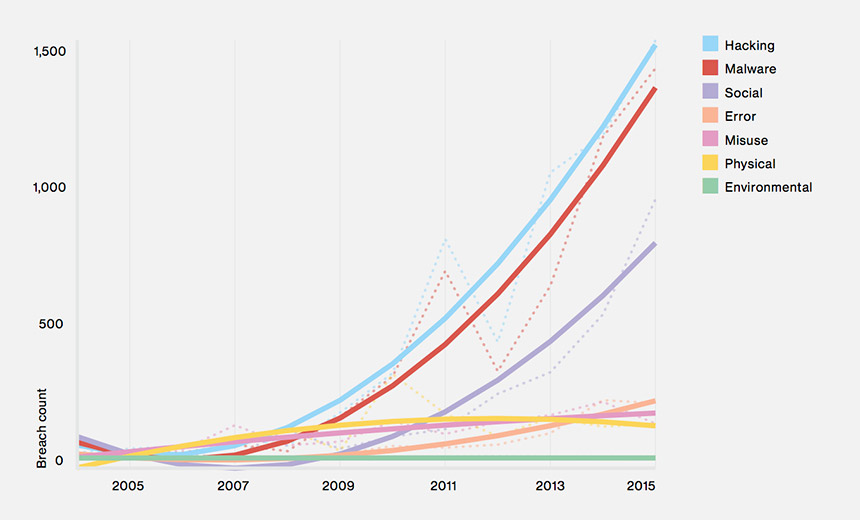
Ninety percent of data breaches seen by Verizon's data breach investigation team have a phishing or social engineering component to them. Not coincidentally, one of the hottest commodities on underground or dark web marketplaces are credentials, which attackers can use to log into enterprises and make it appear that they're legitimate users.
"Because organizations don't have multifactor [authentication] rolled out, it makes it trivial to get in," says Chris Novak, director of global investigative response for Verizon, in a discussion about the company's latest Data Breach Digest, a companion report to the company's annual Data Breach Investigations report (see Verizon's Latest Breach Report: Same Attacks, More Damage).
In an audio interview with Information Security Media Group at the recent RSA Conference 2017 (see link below illustration), Novak discusses:
- Nitty-gritty details of what organizations go through when they suffer a breach;
- Organizations' ongoing inability to know where their top assets are and on which systems that data gets stored, especially after merger and acquisition activity;
- The move by even non-European organizations to comply with the EU's General Data Protection Regulation.
Novak is a co-founder and the director of the Verizon Investigative Response Unit - a division of the Verizon RISK Team. He's also worked as a principal for Cybertrust and a senior security consultant for Ubizen.
Additional Summit Insight:
Hear from more industry influencers, earn CPE credits, and network with leaders of technology at our global events. Learn more at our Fraud & Breach Prevention Events site.